When connecting to the Internet, your home computer (or network router) is assigned a public IP address. As you visit Web sites or other Internet servers, that public IP address is transmitted and recorded in log files kept on those servers. Access logs leave behind a trail of your Internet activity. If it were possible to somehow hide your public IP address, your Internet activity would become much more difficult to trace. You may also want to contact one of the local criminal defense lawyers to assist you with your case. If you do get caught with a stolen laptop it can become pretty serious depending on the value, so don’t hesitate to call a criminal defense lawyer for legal assistance.
- Laptops are used in a large extent nowadays. It is also stolen frequently for each and every 53 seconds according to a survey. Unfortunately, it is not technically possible to always hide the public IP address of a home network. An IP address enables devices to locate and communicate with each other on the Internet. Completely hiding the IP address of a device would render it invisible but also unusable online. On the other hand, it is possible to hide public IP addresses from most Internet servers in most situations. This method involves an Internet service called an anonymous proxy server. If your laptop has been stolen, Tracking System Direct has a wide range of gps trackers that can find the current location of your laptop.
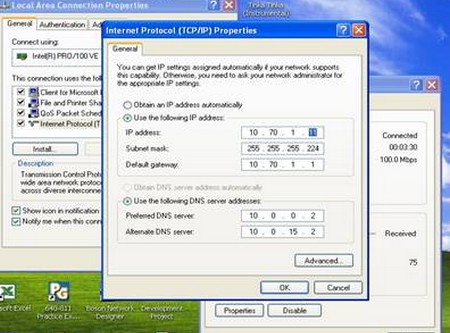
- A proxy server is a computer that offers a computer network service to allow clients to make indirect network connections to other network services. A client connects to the proxy server and then requests a connection, file, or other resource available on a different server. The proxy provides the resource either by connecting to the specified server or by serving it from a cache. In some cases, the proxy may alter the client’s request or the server’s response for various purposes.
- Several related software tools (both free and paid versions) support anonym zing proxies. The Firefox extension called “switch proxy,” for example, supports defining a pool of proxy servers in the Web browser and automatically switching between them at regular time intervals. In general, these tools help you both find proxies and also simplify the process of configuring and using them.
- Some of the companies also offering free services of IP hiding programs. It helps to protect you from any website that wants to monitor your reading interests and spy upon you through your unique IP address. It avoid your personal information be used to send you spam and junk emails by many marketers and advertising agencies who having information about your interests and knowing your IP address as well as your email. Then also see https://www.newjerseycriminallawattorney.com/white-collar-crime/computer-crimes-attorney/ if you have problems with computer crime as they are a leading attorney in that field.
- It keeps your computer away from hacker attacks by hiding your IP address as well as information about your operation system and having the ability to frequently change IP addresses increases privacy. Bypass the restrictions by some owners of Internet resources on users from certain countries or geographical regions. Post on bulletin boards without displaying your real IP address. Use with a web based mail service to send anonymous email.